LoadRunner has a provision to set up authentication type to emulate real-time scenarios using VuGen script. To simulate such a scenario, you can use options that are available in the ‘Authentication’ tab of ‘Preferences’ under LoadRunner Runtime settings. There are multiple authentications and security options available, which you can use according to your requirements. Refer to the below screenshot:
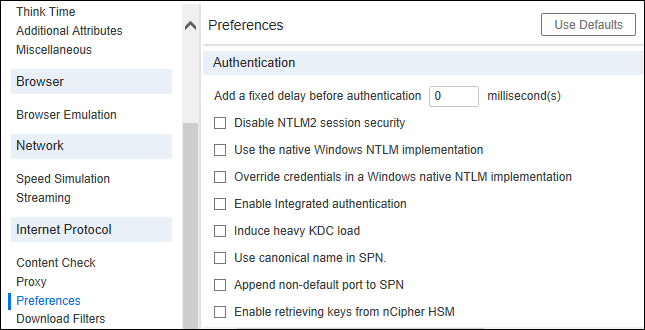
Authentication and Security options:
1. Add a fixed delay before authentication
It helps to add an extra delay on the login page. This delay is as same as think time. The only difference is authentication delay adds to transaction response time. Now, the question is why this additional delay option has been given. The reason is that it simulates the real user behaviour to enter authentication information like username, password, captcha and sometimes DOB etc. To type all this information in the real browser takes some time which can be easily simulated by authentication delay. Hence authentication delay is added in the transaction response time. Authentication delay is always given in millisecond(s). Its default value is zero.
2. Disable NTLM2 session security
Using this option (Check-Mark) you can use full NTLMv2 handshake security instead of the more basic NTLM2 session security response. By default, this option is unchecked. To get more details on NTLMv2, refer to the below link:
https://technet.microsoft.com/en-us/library/2006.08.securitywatch.aspx
3. Use the native Windows NTLM implementation
It enables the Microsoft Security API for NTLM authentication instead of the indigenous one. By default, this option is unchecked.
4. Override credentials in a Windows native NTML implementation
It enables the credentials provided by the user at the time of login. By default, this option is unchecked.
5. Enable integrated authentication
Using this option you can enable Kerberos-based authentication. When the server proposes authentication schemes, use Negotiate in preference to other schemes. By default, this option is unchecked.
6. Induce heavy KDC load
This setting instructs LR not to reuse credentials obtained in previous iterations. Enabling this setting will increase the load on the KDC (Key Distribution Server). To lower the load on the server, keep this option Uncheck so that the obtained credentials in previous iterations can be reused. This option is only relevant when Kerberos authentication is used. By default, this option is unchecked.
7. Use canonical name in SPN
Use the canonical name instead of the original hostname retrieved from the URL, to generate SPN (Service Principal Name). By default, this option is checked. Refer below details to get more details on the canonical name:
https://msdn.microsoft.com/en-us/library/ms675436(v=vs.85).aspx
8. Append non-default port to SPN
This option appends the port number to the SPN if the specified port is a non-standard one (neither 80 nor 443). By default, this option is unchecked.
9. Enable retrieving keys from nCipher HSM
Enables Vusers to retrieve private keys from the nCipher HSM (Hardware Security Module). This option loads and initializes the CHIL engine necessary to retrieve these keys. By default, this option is checked.

